Let’s install an SSL-certificate from Let’s Encrypt for Nginx.
Tag Archives: security
Restrict allowed HTTP methods in Nginx
Security vulnerabilities are often exploits of software that fails when trying to deal with unexpected input. Other times they are exploits of a misconfiguration or a service that unintentionally was open to the public.
For the above reasons, we should limit as much as possible what services are exposed to the public and limit as much as possible what they do and accept from the visitors. To follow those security principles, we should only allow the HTTP methods for which we, in fact, provide services. Under all normal circumstances, that would be the methods GET, POST and HEAD.
Block access to PHP files on your WordPress site with Nginx
In your WordPress site, there are directories that include PHP files that visitors should never be able to access directly. They are only there for WordPress to function as an application that runs on your server. But because of WordPress’ directory and file structure, they are kind of accessible to the public. All of them are meant to be part of a larger application – WordPress, that is – and should not cause any harm if called directly – that we know. Some of the files execute some code even when ran standalone. An attacker might know of a clever way to make that code run in an unexpected manner, causing harm. To be on the safe side, we should deny access to all these PHP files from the outside world. Since we block access to them in our Nginx configuration, PHP will still run them as usual and WordPress will work just fine.
Continue reading “Block access to PHP files on your WordPress site with Nginx”
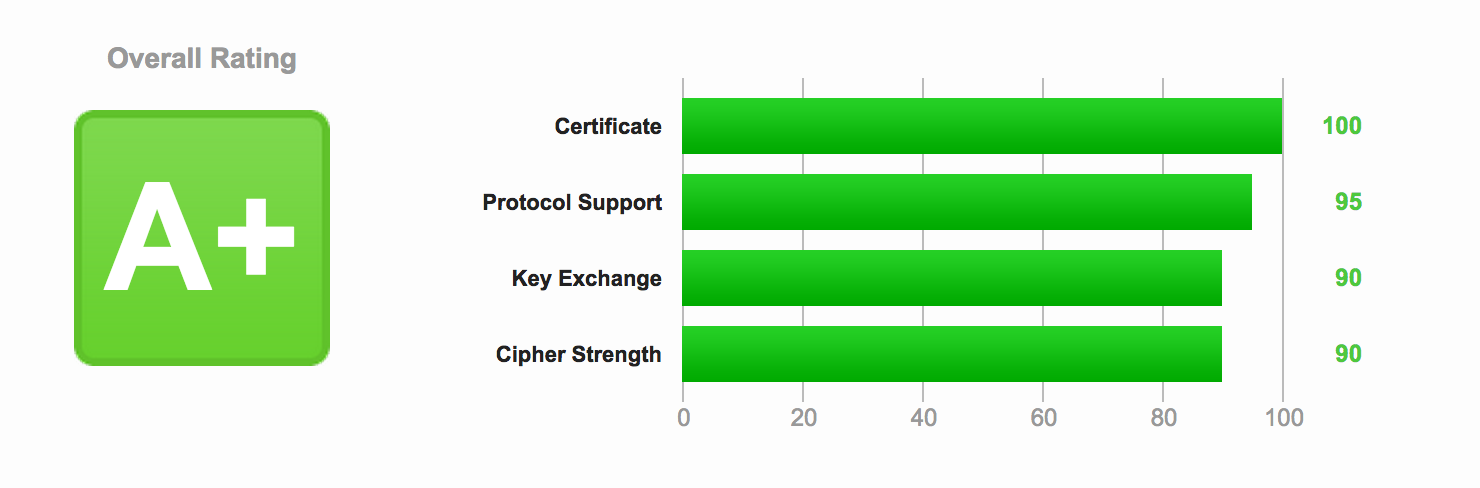
Optimizing HTTPS on Nginx
Now that you have secured Nginx with HTTPS and enabled SPDY enabled HTTP/2, it’s time to improve both the security and the performance of the server.Continue reading “Optimizing HTTPS on Nginx”
Restricting access to WordPress login by IP address
If you have a static IP address, like from your own VPN, it is very easy to increase your security tremendously. Simply restrict all logins to that IP address.
Continue reading “Restricting access to WordPress login by IP address”
Setting up your own PPTP VPN
When it comes to VPNs, there is the choice between PPTP and OpenVPN. PPTP is pretty quick to setup and works out of the box with most (all?) OSes and devices.