Using HTTPS helps preventing someone from snooping your username/password or hijacking your sessions. Using HSTS makes sure the connection stays on HTTPS, even if a MITM tries to redirect you to the plain HTTP version of a web site. But it is easier than you might think for a MITM to use a rogue certificate, making you believe everything is fine. HTTP Public Key Pinning (HPKP) helps the browser check that everything actually is fine.Continue reading “HTTP Public Key Pinning (HPKP)”
Tag Archives: nginx
Running HHVM with fallback to PHP-FPM
HHVM can really speed up your PHP-based web site. Most reports are somewhere in the range of 2–4x faster. Unfortunately, HHVM isn’t very stable and will suddenly die, just of the blue, from time to another. Fortunately, if you’re running Nginx it’s really easy to set up PHP-FPM as a fallback.Continue reading “Running HHVM with fallback to PHP-FPM”
Running HHVM instead of PHP with Nginx on Ubuntu
Since version 3.9, WordPress have been 100% compatible with HHVM and I have begun replacing PHP with it on a few of my servers to experiment.Continue reading “Running HHVM instead of PHP with Nginx on Ubuntu”
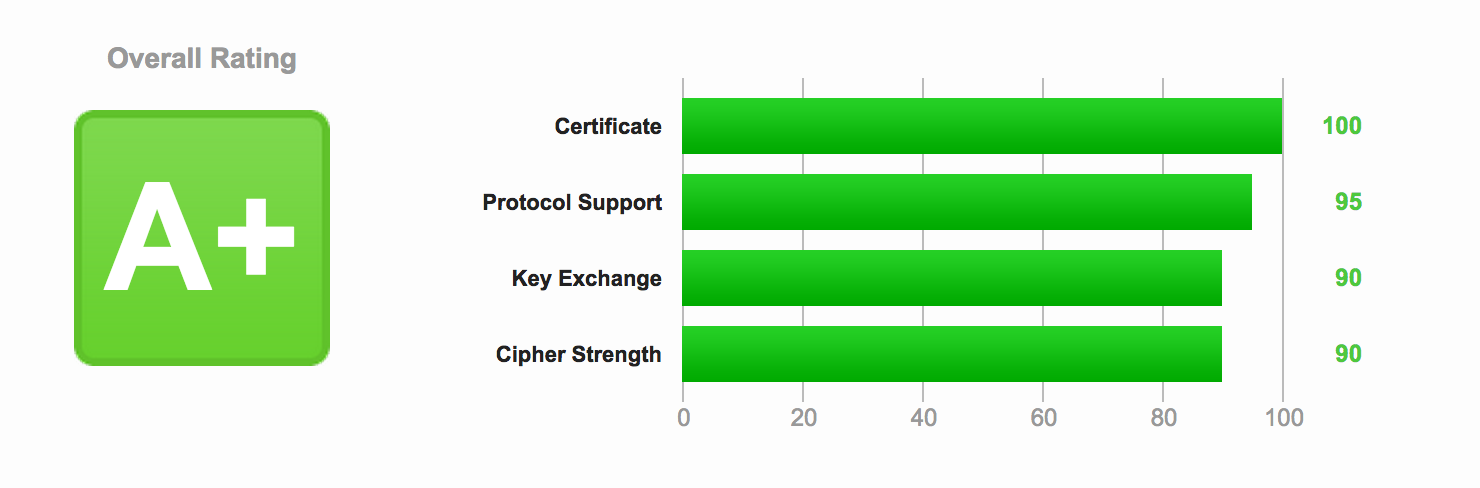
Optimizing HTTPS on Nginx
Now that you have secured Nginx with HTTPS and enabled SPDY enabled HTTP/2, it’s time to improve both the security and the performance of the server.Continue reading “Optimizing HTTPS on Nginx”
Enabling SPDY with Nginx
SPDY is this new, cool, fast protocol created by Google that “replaces” HTTP (the first draft of HTTP 2.0 is using SPDY as the working base). It is supported in all the major browsers – yes, even Internet Explorer – with the exception of Apple’s Safari.Continue reading “Enabling SPDY with Nginx”
Securing Nginx with HTTPS
 Adding a certificate and using the HTTPS protocol is a good improvement to the security in the communication between the browser and the server, and should be in place on all sites that have a user login. Contrary to what many (older) guides say, it doesn’t add much load on your server and is fairy easy and cheap to set up right.Continue reading “Securing Nginx with HTTPS”
Adding a certificate and using the HTTPS protocol is a good improvement to the security in the communication between the browser and the server, and should be in place on all sites that have a user login. Contrary to what many (older) guides say, it doesn’t add much load on your server and is fairy easy and cheap to set up right.Continue reading “Securing Nginx with HTTPS”
Install latest version of Nginx on Ubuntu
![]() I always run the latest LTS version of Ubuntu on all my servers. Unfortunately, the Nginx versions tend to be quite the bit behind the current release. So how do you get an updated, current version of without resorting to having to maintain the packages yourself? Luckily, the Nginx team have their own Ubuntu apt repository so it’s easy to keep current with the latest version of Nginx.Continue reading “Install latest version of Nginx on Ubuntu”
I always run the latest LTS version of Ubuntu on all my servers. Unfortunately, the Nginx versions tend to be quite the bit behind the current release. So how do you get an updated, current version of without resorting to having to maintain the packages yourself? Luckily, the Nginx team have their own Ubuntu apt repository so it’s easy to keep current with the latest version of Nginx.Continue reading “Install latest version of Nginx on Ubuntu”
Restricting access to WordPress login by IP address
If you have a static IP address, like from your own VPN, it is very easy to increase your security tremendously. Simply restrict all logins to that IP address.
Continue reading “Restricting access to WordPress login by IP address”
Caching: Varnish or Nginx?
TL;DR: Varnish lacks support for SSL and SPDY. Nginx handles it just fine, and has very fast cache with either memcache or disk storage (ramdisk). Both can serve stale cache if your backend is down. But Nginx can not write to the memcache storage directly, it has to be done by the application. Also, Nginx can not purge the cache itself, without you compiling your own package.