Let’s install an SSL-certificate from Let’s Encrypt for Nginx.
Category Archives: Security
Restrict allowed HTTP methods in Nginx
Security vulnerabilities are often exploits of software that fails when trying to deal with unexpected input. Other times they are exploits of a misconfiguration or a service that unintentionally was open to the public.
For the above reasons, we should limit as much as possible what services are exposed to the public and limit as much as possible what they do and accept from the visitors. To follow those security principles, we should only allow the HTTP methods for which we, in fact, provide services. Under all normal circumstances, that would be the methods GET, POST and HEAD.
Block access to PHP files on your WordPress site with Nginx
In your WordPress site, there are directories that include PHP files that visitors should never be able to access directly. They are only there for WordPress to function as an application that runs on your server. But because of WordPress’ directory and file structure, they are kind of accessible to the public. All of them are meant to be part of a larger application – WordPress, that is – and should not cause any harm if called directly – that we know. Some of the files execute some code even when ran standalone. An attacker might know of a clever way to make that code run in an unexpected manner, causing harm. To be on the safe side, we should deny access to all these PHP files from the outside world. Since we block access to them in our Nginx configuration, PHP will still run them as usual and WordPress will work just fine.
Continue reading “Block access to PHP files on your WordPress site with Nginx”
Restrict access to the WordPress dashboard by IP address in Nginx
If you have a static IP address, like from your office, or your own private VPN, you can increase your security tremendously by restricting all logins to that IP address. The effect is that even if an attacker knows your login credentials, they will not be able to log in or access any part of the WordPress Dashboard.
Continue reading “Restrict access to the WordPress dashboard by IP address in Nginx”
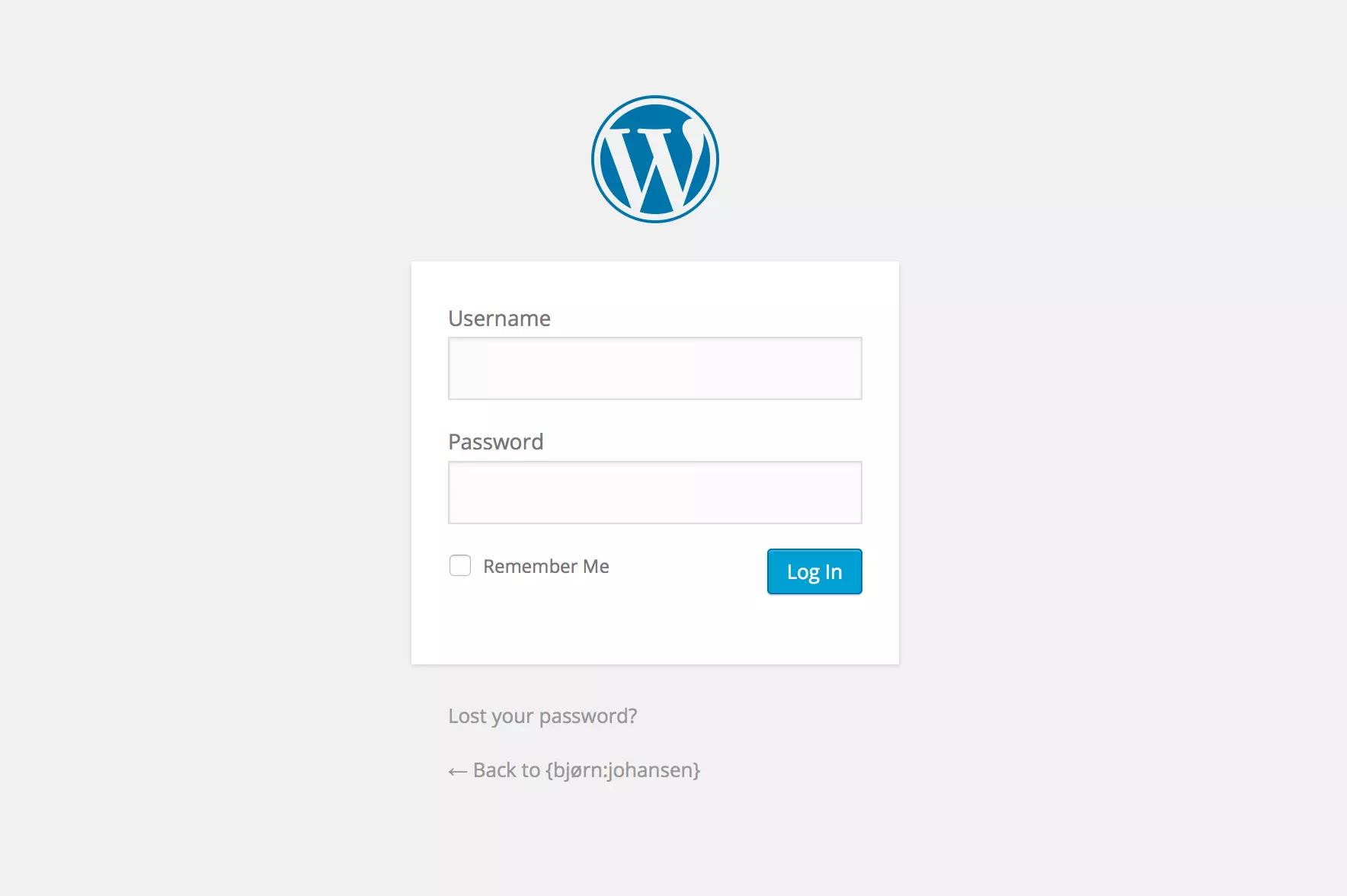
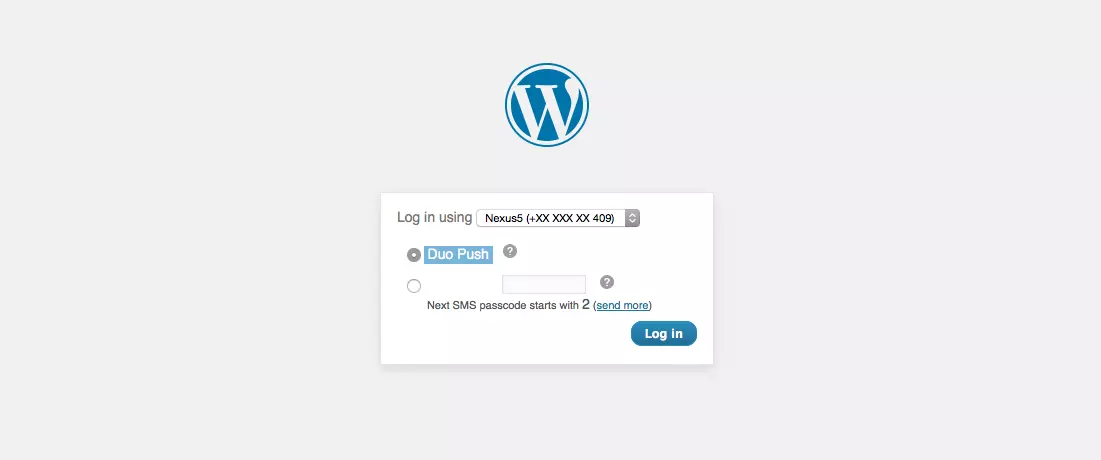
Two Factor Authentication for WordPress
If you’re using a strong password, brute-forcing is a very inefficient way of breaking into your WordPress account, and if it is really strong, dictionary attacks won’t help much either. However, there are are other, easier, ways for a mischievous person to get their hands on your login credentials e.g. with phishing, keyloggers or a MITM attack. By using a two-factor solution, you will increase your login security by an order of magnitude.Continue reading “Two Factor Authentication for WordPress”
HTTP Public Key Pinning (HPKP)
Using HTTPS helps preventing someone from snooping your username/password or hijacking your sessions. Using HSTS makes sure the connection stays on HTTPS, even if a MITM tries to redirect you to the plain HTTP version of a web site. But it is easier than you might think for a MITM to use a rogue certificate, making you believe everything is fine. HTTP Public Key Pinning (HPKP) helps the browser check that everything actually is fine.Continue reading “HTTP Public Key Pinning (HPKP)”
Using fail2ban to block WordPress login attacks
Fail2ban works by filtering a log file with a regular expression triggering a ban action if the condition is met. After a preset time, it will trigger an unban action. Without much effort, we can have WordPress log all authentication events and have fail2ban react on them.Continue reading “Using fail2ban to block WordPress login attacks”
Using fail2ban from behind a Rackspace Cloud LoadBalancer
If your fail2ban is on a host behind a Rackspace Cloud LoadBalancer, you’ll want to block the offending IP addresses directly in your LoadBalancer. If your LB is acting as a reverse proxy, you’ll HAVE to block in the LB, but it is also nice to protect all other nodes behind the LB and offload the lifting.Continue reading “Using fail2ban from behind a Rackspace Cloud LoadBalancer”
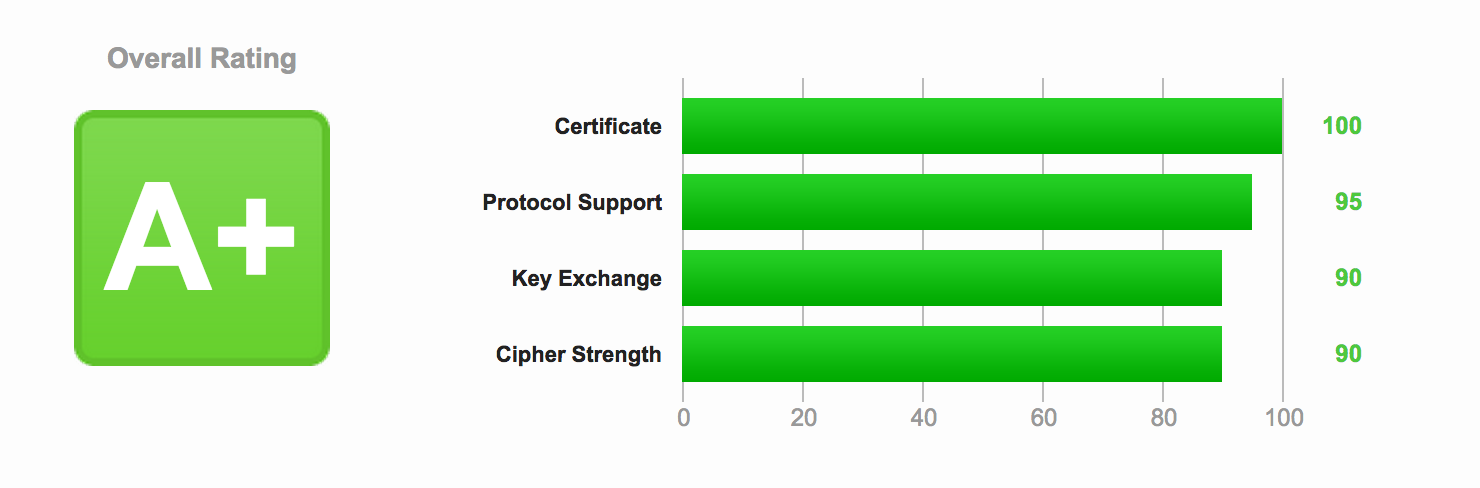
Optimizing HTTPS on Nginx
Now that you have secured Nginx with HTTPS and enabled SPDY enabled HTTP/2, it’s time to improve both the security and the performance of the server.Continue reading “Optimizing HTTPS on Nginx”
Securing Nginx with HTTPS
 Adding a certificate and using the HTTPS protocol is a good improvement to the security in the communication between the browser and the server, and should be in place on all sites that have a user login. Contrary to what many (older) guides say, it doesn’t add much load on your server and is fairy easy and cheap to set up right.Continue reading “Securing Nginx with HTTPS”
Adding a certificate and using the HTTPS protocol is a good improvement to the security in the communication between the browser and the server, and should be in place on all sites that have a user login. Contrary to what many (older) guides say, it doesn’t add much load on your server and is fairy easy and cheap to set up right.Continue reading “Securing Nginx with HTTPS”